$430M in One Month: Why AI Agent Security Is 2026's Hottest VC Category
March 2026 saw $430M+ invested in AI agent security across 5 major rounds. Combined with 30 CVEs, 9 documented MCP breaches, and 1,184 malicious skills, the market signal is unmistakable.

In March 2026, venture capital firms collectively poured over $430 million into AI agent security startups across five major funding rounds. This is not a coincidence. It is the market pricing in a reality that practitioners have been warning about for months: AI agents are everywhere, they are deeply integrated into enterprise infrastructure, and the security tooling has not kept pace.
This post breaks down the numbers, the threat landscape driving the investment, what these funded companies are actually building, and what the open-source ecosystem is doing in parallel.
The Numbers: $430M in Five Rounds
March 2026 will be remembered as the month AI agent security became a formal VC category. Here are the five rounds that defined it:
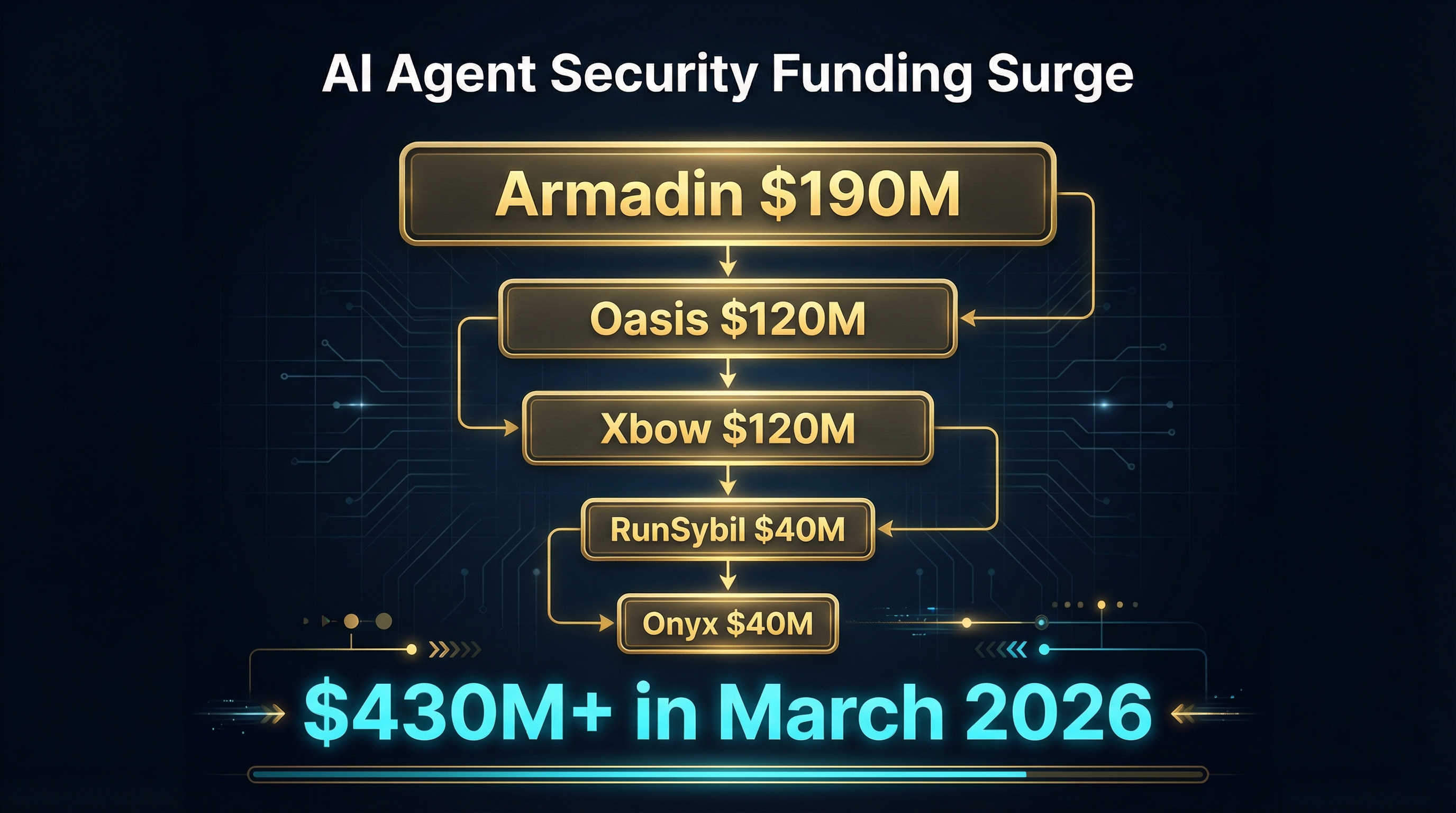
Armadin — $190M Series B. Founded by Kevin Mandia (Mandiant founder and former FireEye CEO), Armadin raised the largest round of the month. Their thesis is straightforward: the same threat detection and incident response discipline that Mandiant built for network security needs to be rebuilt for agentic AI. Armadin’s platform monitors agent-to-tool interactions in real time, applying behavioral analysis to detect anomalous patterns — an agent suddenly requesting credentials it has never accessed before, or a tool returning schemas that differ from its registered baseline. Mandia’s track record gives this round significant weight. When the person who built one of the defining companies in network threat intelligence pivots to agent security, the signal is hard to ignore.
Oasis Security — $120M Series B (Sequoia, Accel). Oasis is attacking the identity and access management problem for non-human entities. Their core argument: enterprises have spent two decades building IAM for human users, but AI agents operate outside those frameworks entirely. An agent connecting to an MCP server does not authenticate the way a human logs into a SaaS product. Oasis provides identity governance for machine-to-machine interactions — tracking which agents have access to which tools, enforcing least-privilege policies, and maintaining audit trails for compliance. The Sequoia and Accel co-lead signals that tier-one investors see identity governance for agents as a foundational infrastructure layer, not a niche product.
Xbow — $120M Series A (unicorn valuation). Xbow is building autonomous red-teaming for AI systems. Rather than relying on human penetration testers to probe agent deployments, Xbow uses AI agents to attack other AI agents — systematically testing for prompt injection, tool poisoning, privilege escalation, and data exfiltration vulnerabilities. Their platform generates adversarial test suites tailored to specific agent architectures, runs them continuously, and reports exploitable vulnerabilities before attackers find them. Reaching unicorn status at Series A is notable. It reflects the market’s expectation that offensive security testing for AI agents will become as standard as penetration testing is for web applications today.
RunSybil — $40M Series A (backed by OpenAI and Anthropic). RunSybil focuses on runtime monitoring and anomaly detection for deployed agents. What makes them distinctive is their investor base: both OpenAI and Anthropic participated in the round. When the two largest foundation model providers both invest in a security company, they are signaling that they recognize the security gap between model capabilities and deployment safety. RunSybil’s platform sits between the agent and its tool providers, inspecting every interaction for signs of manipulation, data leakage, or unauthorized access patterns.
Onyx — $40M Seed. Onyx is the earliest-stage company in this cohort but targets a critical gap: supply chain security for MCP servers and agent tool registries. Their approach combines static analysis, behavioral sandboxing, and community reputation scoring to evaluate MCP servers before they are connected to production agents. Think of it as a security scanner specifically designed for the MCP ecosystem — inspecting tool definitions, monitoring for schema drift, and flagging servers that exhibit suspicious behavior patterns.
Why Now: The Threat Landscape Forced the Market’s Hand
These funding rounds did not happen in a vacuum. Three converging data points made the investment thesis undeniable.
9 Documented MCP Breaches
AuthZed’s March 2026 threat report documented nine confirmed breaches where MCP server vulnerabilities were the primary attack vector. These ranged from credential harvesting through malicious tool descriptions to full lateral movement through agent-to-agent communication channels. The Clinejection attack chain from January — where a crafted GitHub issue title triggered a code assistant to install a poisoned npm package, compromising approximately 4,000 developer machines — was the incident that moved agent security from “theoretical concern” to “active threat” in most enterprise risk assessments.
Several of the nine breaches involved attacks on the trust boundary between multiple MCP servers. An agent connected to both a data source server and an execution server could be manipulated by the data source to issue commands through the execution server. No individual server was compromised; the vulnerability existed in the composition. This class of attack is particularly difficult to defend against because each component passes a security audit in isolation.
30 CVEs in 60 Days
Between mid-January and mid-March 2026, thirty CVEs were filed against MCP-related software — servers, client libraries, registries, and agent frameworks. This represents a sharp acceleration from 2025, which saw fewer than 20 MCP-related CVEs for the entire year. The CVEs cover the full spectrum: authentication bypasses, schema injection vulnerabilities, insufficient input validation on tool responses, and privilege escalation through capability negotiation.
The volume matters because it indicates that security researchers are actively probing MCP infrastructure and finding substantive issues. This is the pattern that preceded major security investment in cloud infrastructure (2014-2016), container security (2017-2019), and API security (2020-2022). When CVE counts spike, VC dollars follow within one to two quarters.
1,184 Malicious OpenClaw Skills
OpenClaw, the largest open MCP skill registry, conducted an internal audit in February 2026 and found 1,184 skills that exhibited malicious behavior. This represented approximately 8% of the total registry at the time. The malicious skills employed a range of techniques: tool description manipulation to influence agent behavior, credential exfiltration disguised as legitimate API calls, and data harvesting through overly broad schema definitions.
The OpenClaw finding echoed earlier research from Grith.ai, which found that 12% of audited agent skills across all major registries qualified as malicious. The consistency of these numbers across independent audits is significant. It means that any agent connecting to a public registry without pre-screening has roughly a one-in-ten chance of loading a malicious tool.
Together, these three data points — active breaches, accelerating CVEs, and demonstrated registry compromise at scale — created a market signal that venture capital could not ignore.
What These Companies Are Building
The five funded companies map to distinct layers of the agent security stack:
Threat detection and response (Armadin): real-time monitoring of agent behavior to detect and respond to active attacks. This is the equivalent of an EDR platform for AI agents — watching every tool call, every data flow, and every permission change for signs of compromise.
Identity and access governance (Oasis Security): managing which agents can access which tools under which conditions. Enterprise IT teams need the same level of identity management for their AI agents that they have for human users — role-based access, least privilege enforcement, session management, and comprehensive audit logging.
Offensive security testing (Xbow): continuous red-teaming that probes agent deployments for vulnerabilities before attackers find them. Automated adversarial testing is essential because the attack surface changes every time a new MCP server is connected or an existing one updates its schemas.
Runtime monitoring (RunSybil): inspecting agent-tool interactions as they happen, detecting anomalies, and enforcing security policies at the communication layer. This is particularly important for catching composition attacks where the vulnerability emerges from the interaction between multiple legitimate components.
Supply chain security (Onyx): scanning and vetting MCP servers and tool registries before they are connected to production agents. Addressing the registry poisoning problem at the source rather than trying to detect malicious behavior after connection.
The layered nature of these investments is important. No single product addresses all attack vectors. The VC market appears to be funding a full security stack, similar to how cloud security evolved from individual point products into a layered defense-in-depth architecture.
The Open-Source Response
Venture-funded startups are not the only ones building agent security tooling. A parallel open-source ecosystem is developing solutions that address many of the same problems, often with different architectural approaches.
MCPProxy is an open-source MCP gateway that implements schema quarantine and BM25-based tool discovery. When a new MCP server connects, MCPProxy quarantines its tools — analyzing schemas for known attack patterns and testing behavior in isolation before making tools available to agents. The BM25 scoring limits which tools are presented for any given query, reducing the context explosion problem and limiting the attack surface per interaction. MCPProxy also provides request-level access controls and audit logging.
Sentrial takes a policy-as-code approach to agent security. Teams define security policies in a declarative format — specifying which tool behaviors are acceptable, what data can flow between which endpoints, and under what conditions tool access should be revoked. Sentrial evaluates every agent interaction against these policies in real time, blocking or flagging violations.
MCPDome focuses on network-level protection for MCP communications. It acts as a security proxy that inspects and filters traffic between agents and MCP servers, applying TLS verification, rate limiting, and payload inspection. MCPDome addresses the network security layer that most agent frameworks leave unprotected.
Golf Scanner is an open-source static analysis tool specifically designed for MCP server definitions. It scans tool schemas, descriptions, and capability declarations for known malicious patterns — injection vectors in descriptions, overly broad permission requests, and schemas that attempt to exfiltrate data through input validation. Think of it as a linter for MCP security, designed to run in CI/CD pipelines before MCP servers are deployed or connected.
These open-source projects share a common philosophy: security tooling for agents should be transparent, auditable, and accessible to teams that cannot afford enterprise security platforms. The code is visible, the detection rules are public, and the community can contribute new defenses as new attack patterns emerge.
The relationship between the VC-funded and open-source ecosystems is not purely competitive. Several of the funded companies have acknowledged open-source tools in their technical documentation, and there is meaningful cross-pollination of ideas. The open-source projects tend to move faster on specific technical problems (schema quarantine patterns, BM25 filtering approaches), while funded companies invest in enterprise features (SSO integration, compliance reporting, managed deployment).
What This Means for Practitioners
If you are building or deploying AI agents in production, here is what the $430M signal means for your work:
Agent security is no longer optional. The combination of VC investment, CVE volume, and documented breaches means that enterprise procurement will start requiring security controls for agent deployments. If your agents connect to external MCP servers without pre-screening, runtime monitoring, or access controls, you are accumulating technical debt that will become a compliance liability.
Defense in depth applies to agents. No single tool — funded or open-source — addresses the full attack surface. A reasonable minimum security posture includes: pre-connection screening of MCP servers (schema quarantine or static analysis), runtime monitoring of agent-tool interactions, identity management and least-privilege access controls, and regular adversarial testing. Layer your defenses the same way you would for any other critical infrastructure.
Evaluate your registry exposure. The 1,184 malicious skills finding means that connecting agents to public registries without filtering is a measurable risk. Whether you use a commercial vetting service or an open-source scanner, every MCP server should be evaluated before it reaches your agents.
Watch the composition boundary. The most sophisticated attacks target the interaction between multiple legitimate tools, not individual tools in isolation. When your agent is connected to both a data source and an execution environment, you need security controls that understand the combined behavior, not just the individual components.
Start with what is available today. You do not need to wait for the funded companies to ship their products. Open-source tools like MCPProxy, Sentrial, MCPDome, and Golf Scanner are available now and address the most critical security gaps. Start with schema quarantine and access controls, then add runtime monitoring and adversarial testing as your deployment matures.
The Bigger Picture
The $430M invested in AI agent security in March 2026 is not just a VC trend. It is the market recognizing that agentic AI has crossed the threshold from experimental technology to critical infrastructure — and that critical infrastructure requires security investment proportional to the risk it carries.
The parallel development of funded companies and open-source tools suggests that the ecosystem is maturing in a healthy way. Enterprises will have options at every price point and every layer of the security stack. The practitioners who act now — adopting layered defenses, evaluating their registry exposure, and building security into their agent architectures from the start — will be ahead of the compliance requirements that are inevitably coming.
The money has spoken. Agent security is not a niche concern. It is the next foundational layer of AI infrastructure.