MCP Security Just Became an Enterprise Product Category
In five days, three companies launched dedicated MCP security products. Combined with OWASP MCP Top 10 and CoSAI's threat taxonomy, MCP security has transitioned from research concern to funded enterprise market.

Between March 12 and March 17, 2026, three companies launched dedicated MCP security products within five days of each other. SurePath AI shipped real-time MCP policy controls. PointGuard AI unveiled a full MCP Security Gateway. Proofpoint acquired Acuvity and announced an intent-based AI security platform with MCP agent coverage. None of these companies coordinated their launches. They all arrived at the same conclusion independently: the Model Context Protocol has created an attack surface large enough to sustain a commercial security market.
This is not a speculative trend piece. The products are shipping. The budgets are allocated. MCP security is now an enterprise product category with funded vendors, differentiated positioning, and real customers. Here is what happened, what the products actually do, and what it means for practitioners choosing between commercial and open-source options.
Five Days That Changed the Market
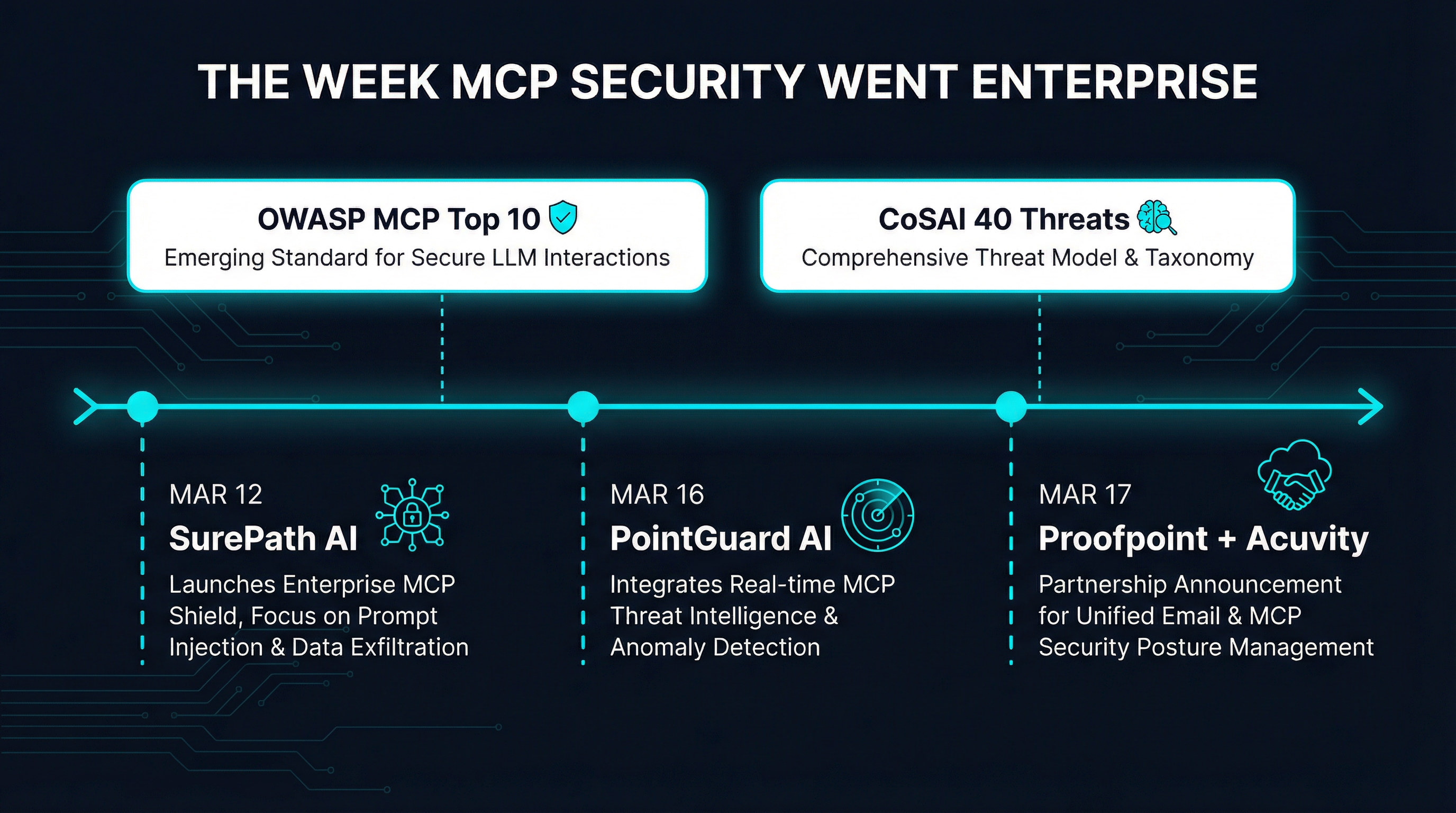
The sequence started on March 12 when SurePath AI announced real-time MCP policy controls. Their product intercepts MCP tool calls before execution, applies block/allow lists, and classifies tools as well-known or custom-built. Randy Birdsall, their CPO and co-founder, framed it bluntly: “MCP introduces an entirely new attack surface. Modern organizations need controls specific to how MCP operates.”
Four days later, on March 16, PointGuard AI launched what they called “the first AI security platform with a fully integrated MCP Gateway.” Their product goes beyond tool-level policy to include intent-based zero-trust authorization, AI-native data loss prevention, and a centralized inventory of agents, MCP servers, and tools. The positioning was aggressive — they claimed to offer “the most complete, enterprise-class AI security platform available today.”
Then on March 17, Proofpoint announced their entry through the acquisition of Acuvity. The resulting product, Proofpoint AI Security, introduced what they call the Agent Integrity Framework — a five-phase maturity model spanning discovery through runtime enforcement. CEO Sumit Dhawan stated the obvious: “AI is now embedded in how work gets done, and security must evolve with it.”
These launches did not emerge in a vacuum. The OWASP MCP Top 10 project had already codified the ten most critical MCP security risks. CoSAI, the Coalition for Secure AI (an OASIS Open project), published a white paper in January 2026 identifying an extensive taxonomy of MCP security threats and urging standardized security practices for AI agents connecting to external tools. The research foundation was laid months ago. The commercial market built on top of it.
The Converging Feature Set
Despite different positioning and go-to-market strategies, the three products converge on a remarkably similar architectural pattern. All three implement gateway-level interception — a proxy that sits between AI agents and MCP servers, inspecting and enforcing policy on every tool call before it reaches the downstream system.
Tool-call authorization is the baseline feature across all three. SurePath AI implements this through block/allow lists with a read-only mode that permits non-destructive tools by default. PointGuard AI takes a more granular approach with per-agent, per-tool, per-workflow least-privilege policies that distinguish between read, write, and update operations. Proofpoint evaluates whether each AI action aligns with the original request, defined policies, and intended purpose.
Data loss prevention for agent outputs is the second convergence point. When an AI agent queries a database, summarizes a document, or generates a report through MCP tools, the output passes through the gateway before reaching the user or downstream system. PointGuard AI’s DLP inspects outbound responses for sensitive information and can block, mask, or redact data. Proofpoint observes prompts, responses, and data flows during AI interactions and applies access controls in real time. SurePath AI’s approach focuses on removing blocked or policy-violating tools from payloads entirely, preventing the exposure from occurring in the first place.
Discovery and inventory is the third shared capability. Organizations deploying MCP at scale need to know what agents exist, what MCP servers they connect to, and what tools those servers expose. All three vendors provide centralized visibility. Proofpoint discovers both sanctioned and unsanctioned AI tools including local models, ChatGPT instances, and MCP servers. PointGuard AI maintains a context-aware inventory that evaluates trust relationships between agents, servers, and data sources. SurePath AI’s auto-discovery classifies tools and identifies whether they are well-known community servers or custom-built internal ones.
The shared architecture is not coincidental. These companies are responding to the same threat landscape documented by OWASP and CoSAI. The attack vectors — tool poisoning, privilege escalation through scope creep, cross-tenant context leakage, intent flow subversion — all require inspection at the gateway layer because they exploit the protocol’s own communication channels. Network-level firewalls cannot see inside MCP tool calls. Endpoint security cannot evaluate whether a tool response contains injected instructions. The gateway pattern is emerging as the only viable enforcement point.
The Context Window Problem
There is a related technical challenge that the enterprise products have begun to address, though none have fully solved it: context window waste. Every MCP tool call includes a schema definition that the LLM must process — parameter descriptions, type annotations, usage examples. When an agent has access to dozens or hundreds of tools, the cumulative token cost of simply describing those tools to the model can consume a significant fraction of the available context window.
Benchmarks in the MCP ecosystem have measured context overhead approaching 72% in deployments with large tool registries. That means nearly three-quarters of the LLM’s processing capacity is spent understanding what tools exist rather than doing useful work. This is not a security problem per se, but it is an operational cost that compounds with every additional security layer. Gateway products that add their own metadata — policy annotations, audit flags, enforcement results — can make the problem worse if they are not disciplined about token economy.
SurePath AI’s approach of stripping blocked tools from the payload before it reaches the agent is one mitigation. If a tool is not permitted, the agent never sees it, saving the context tokens that would have been wasted describing it. PointGuard AI’s centralized inventory could theoretically support similar optimization by pre-filtering tool lists based on the agent’s role. But none of the three vendors have positioned context efficiency as a primary feature. For organizations running at scale, this is worth watching.
Open Source vs. Enterprise: An Honest Comparison
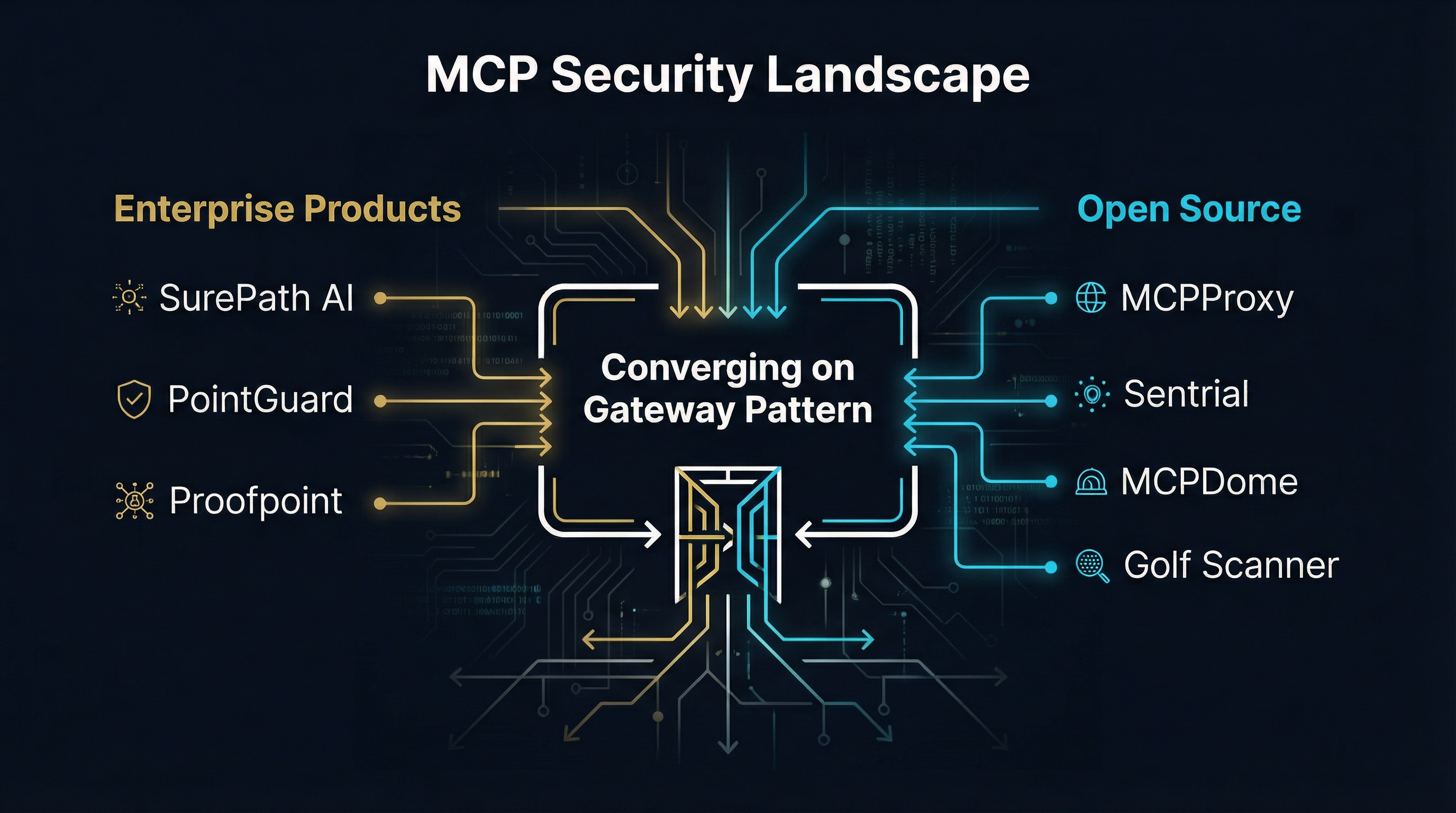
The commercial launches raise an obvious question: what about open-source alternatives? Several projects implement overlapping functionality without the enterprise price tag.
MCPProxy is a Go-based gateway that implements BM25 tool discovery, quarantine for untrusted servers, and Docker-based isolation. It addresses the context window problem directly through intelligent tool routing — only surfacing relevant tools based on the current query rather than dumping the entire tool registry into context. Sentrial focuses on runtime security monitoring for MCP connections. MCPDome provides sandboxed execution environments. Golf Scanner takes a different approach entirely, focusing on vulnerability scanning of MCP server configurations before deployment.
The honest comparison between these categories breaks down along predictable lines:
Where enterprise products win. Compliance reporting, audit trails, and integration with existing SIEM/SOAR infrastructure. If your organization needs to demonstrate MCP security controls to auditors, document policy enforcement for SOC 2, or feed agent activity logs into Splunk, the commercial products are purpose-built for this. Open-source tools can produce logs, but transforming those logs into compliance artifacts requires significant custom engineering. Enterprise products also offer managed deployment, SLA guarantees, and dedicated support — table stakes for organizations that cannot afford to debug open-source gateway failures at 3 AM during an incident.
Where open source wins. Transparency, customization, and cost. You can read every line of MCPProxy’s enforcement logic. You can modify quarantine rules, add custom tool validators, or integrate with internal authorization systems without waiting for a vendor’s feature roadmap. For teams with strong engineering capacity, this flexibility is worth more than any commercial feature. Open-source tools also avoid vendor lock-in — a real concern when the MCP security market is less than a week old and consolidation is inevitable.
Where neither wins yet. Cross-organizational trust federation. When multiple companies need to share MCP servers while maintaining independent security policies, neither commercial nor open-source tools have a mature solution. This is the multi-tenant problem that OWASP MCP02 and MCP09 describe, and it will likely require protocol-level changes rather than gateway-layer workarounds.
The reality is that most organizations will end up using both. An open-source gateway like MCPProxy for development and internal tooling, where flexibility and cost matter most, alongside an enterprise product for production workloads that touch customer data and require compliance documentation. This is not unlike the broader security tooling landscape, where open-source intrusion detection (Suricata, Zeek) coexists with commercial EDR platforms (CrowdStrike, SentinelOne) in the same organization.
What Practitioners Should Do Now
The market transition from “MCP security is a research concern” to “MCP security is a funded enterprise category” happened faster than most teams anticipated. If you are deploying MCP in any capacity — even for internal tooling — here is a practical checklist.
Inventory your MCP surface area. Before evaluating any security product, you need to know what you are protecting. How many MCP servers are your agents connecting to? Which are community-maintained and which are internal? What tools do they expose, and what data can those tools access? You cannot secure what you have not cataloged.
Implement gateway-level inspection now, not later. Whether you choose a commercial product or an open-source gateway, the architectural pattern of inspecting tool calls at a proxy layer is the consensus approach across both OWASP recommendations and every vendor in this space. Retrofitting gateway inspection into an existing deployment is harder than starting with it. If you are building new agent infrastructure, put the gateway in from day one.
Separate tool authorization from tool discovery. The fact that an agent knows a tool exists should not mean the agent is authorized to use it. This is the core principle behind SurePath AI’s block/allow lists, PointGuard AI’s per-agent least-privilege policies, and MCPProxy’s quarantine system. Implement it regardless of which product you use.
Watch the context window. As you add security layers — policy metadata, audit annotations, enforcement results — monitor the token overhead. A 72% context waste benchmark means your agents are spending most of their capacity on overhead rather than useful work. Tools that optimize tool routing (surfacing only relevant tools per query) will deliver better results than tools that dump everything into context and hope the model figures it out.
Do not bet on one vendor yet. The MCP security market is five days old. At least one of these three vendors will be acquired within 18 months. At least one will pivot. The protocol itself is still evolving, with the MCP spec continuing to add capabilities that will reshape the threat surface. Maintain optionality. Use open-source tools to build institutional knowledge about MCP security patterns, and evaluate commercial products for specific compliance requirements rather than wholesale delegation.
The Bigger Picture
What happened in the week of March 12-17 was not just three product launches. It was the market acknowledging that AI agents interacting with enterprise systems through standardized protocols create a security surface that existing tools cannot address. Firewalls do not inspect tool calls. IAM systems do not understand agent delegation. DLP products do not scan MCP responses for injected instructions.
The OWASP MCP Top 10 gave the problem a taxonomy. CoSAI’s threat analysis gave it academic rigor. SurePath AI, PointGuard AI, and Proofpoint gave it a price tag. The open-source ecosystem — MCPProxy, Sentrial, MCPDome, and others — gave it an accessible entry point.
MCP security is no longer something you can defer to next quarter’s roadmap. The attack surface is documented. The exploits are proven. The products exist. The only remaining question is whether your organization will implement controls proactively or reactively. History suggests most will choose the latter, but the tools to choose the former are now available across both commercial and open-source options.
The gateway pattern has won the architectural argument. The remaining debates — commercial vs. open source, agent-level vs. tool-level policy, centralized vs. federated trust — are implementation details. Important implementation details, but details nonetheless. The market has spoken: MCP security is an enterprise product category, and it is here to stay.